- When a Client Device connects to a Network, the device will start sending multiple traffic based on the Applications opened on that device.
- The initial set of traffic triggered by the Client will identify if there is a Captive Portal Authentication configured on that wireless network.
- Let us consider a Windows Client connecting to the Wi-Fi, configured with Internal Captive-Portal Authentication.
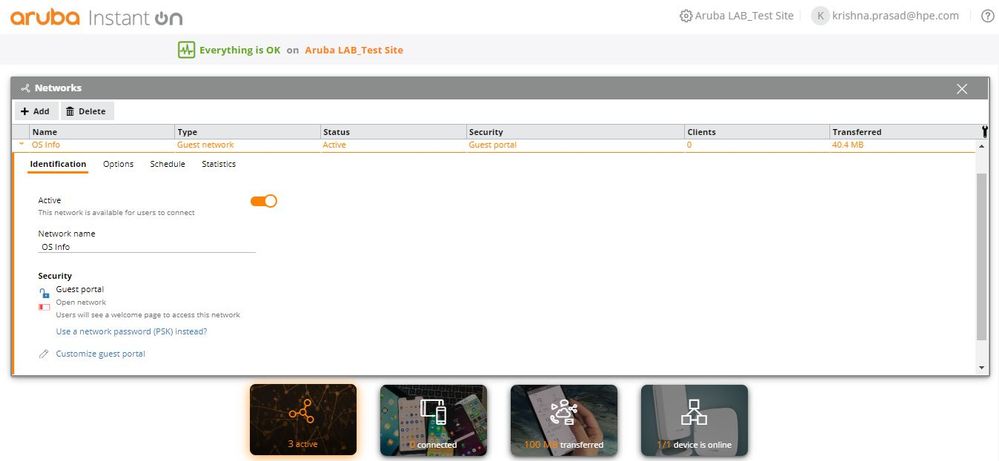 Captive Portal Authentication
Captive Portal Authentication
- Once the Windows Client connects to the Wi-Fi, it initiates a DNS request to www.msftconnecttest.com.
- Similarly, iOS and Android devices have their own FQDN to check the existence of Captive-Portal Authentication in the Wireless Network.
- Check the below posts for more details.
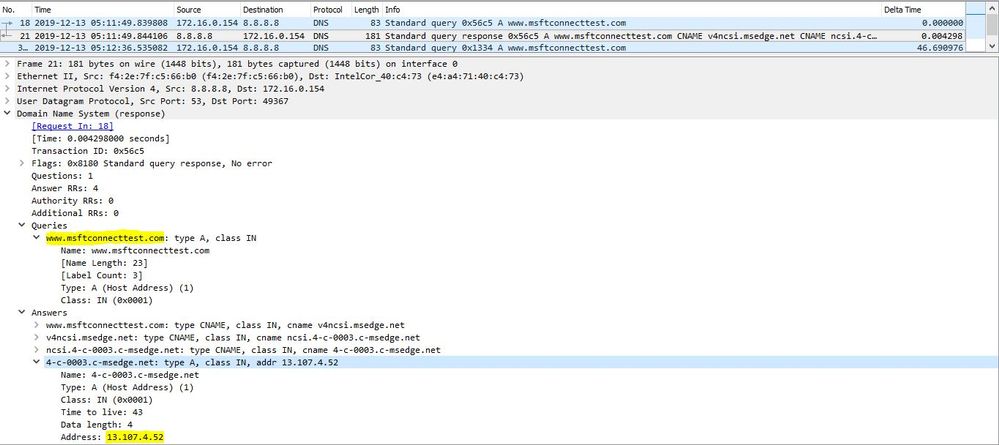 ">www.msftconnecttest.com">DNS Request / Response to www.msftconnecttest.com
">www.msftconnecttest.com">DNS Request / Response to www.msftconnecttest.com
- Once the Client Device gets the IP address of www.msftconnecttest.com through DNS resolution, it will initiate a TCP handshake to that IP address.
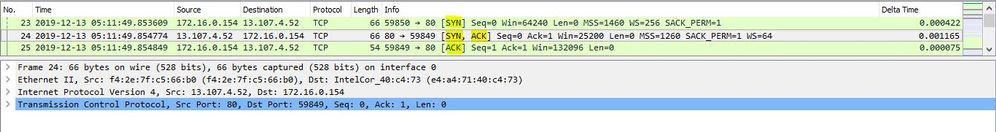 ">www.msftconnecttest.com">TCP Connection to www.msftconnecttest.com
">www.msftconnecttest.com">TCP Connection to www.msftconnecttest.com
- According to the Client Device, it has established a TCP connection with www.msftconnecttest.com.
- But in turn, the Aruba Instant On APs spoofs the TCP connections initiated by the Guest Clients and respond to those TCP connection requests, on behalf of www.msftconnecttest.com.
- The above TCP connection is hence between the Guest Client and the AP.
- Once the TCP connection is established, the Guest Client sends a HTTP Get, to get the webpage of www.msftconnecttest.com.
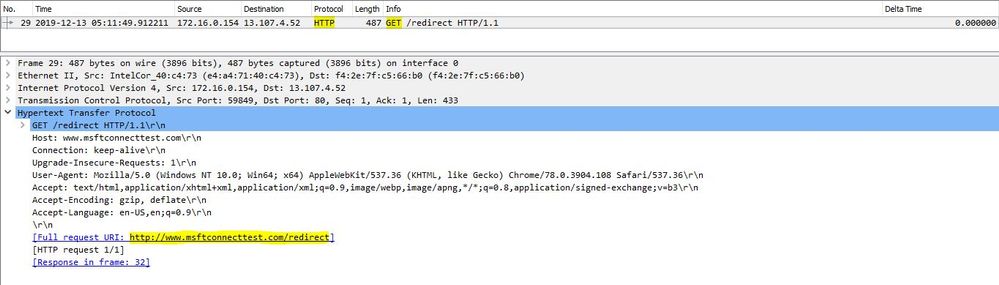 ">www.msftconnecttest.com">HTTP Get request to www.msftconnecttest.com
">www.msftconnecttest.com">HTTP Get request to www.msftconnecttest.com
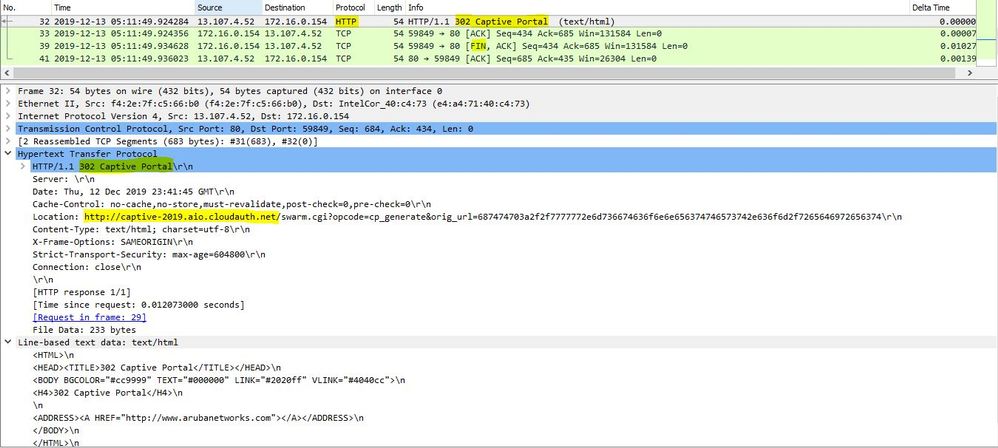 302 Captive Portal redirection and TCP connection termination
302 Captive Portal redirection and TCP connection termination
- The Guest Client then sends out a DNS request to resolve the IP address of URL received through 302 Redirection - http://captive-2019.aio.cloudauth.net/swarm.cgi
- Since this URL belongs to the Aruba Instant On APs, the DNS servers will not have an IP address entry to the above mentioned URL.
- The APs will hence spoof the DNS response from the DNS server and respond back to the Guest Client with the Internal IP address (172.31.98.1) of the AIO AP.
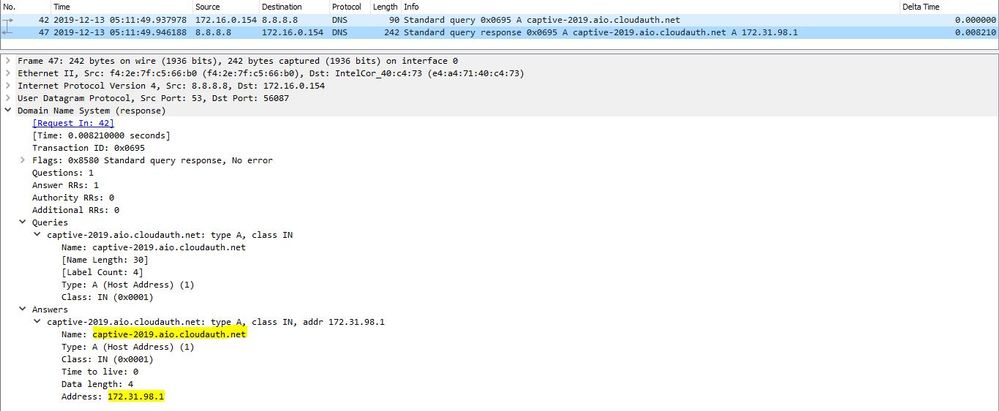 ">http://captive-2019.aio.cloudauth.net/swarm.cgi">DNS Request and Response to resolve the IP address of http://captive-2019.aio.cloudauth.net/swarm.cgi
">http://captive-2019.aio.cloudauth.net/swarm.cgi">DNS Request and Response to resolve the IP address of http://captive-2019.aio.cloudauth.net/swarm.cgi
- The Guest Client will initiate a TCP connection with the AP’s IP address 172.31.98.1 followed by HTTP Get.
- The HTTP Get is for the Guest Client to fetch the Captive Portal Page hosted by the Aruba Instant On AP.
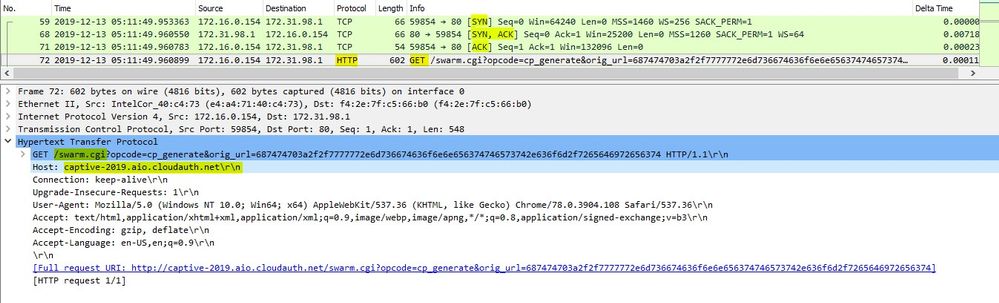 HTTP Get to fetch the Captive Portal Page hosted by the AP
HTTP Get to fetch the Captive Portal Page hosted by the AP
- The Aruba Instant ON AP will send the Captive Portal page to the Guest Client.
- The complete TCP stream when the Guest Client gets the Captive Portal Page is as below.
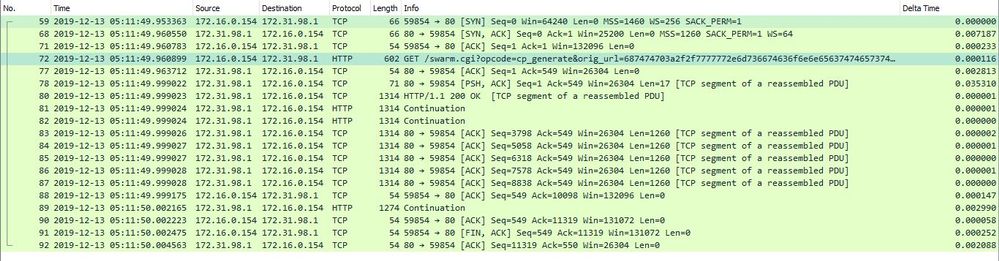 HTTP stream when the Guest Client gets the Captive Portal page
HTTP stream when the Guest Client gets the Captive Portal page
- Below is the Captive Portal page hosted on the test client.
- The TCP connections is terminated by the client once it receives the Captive Portal Page.
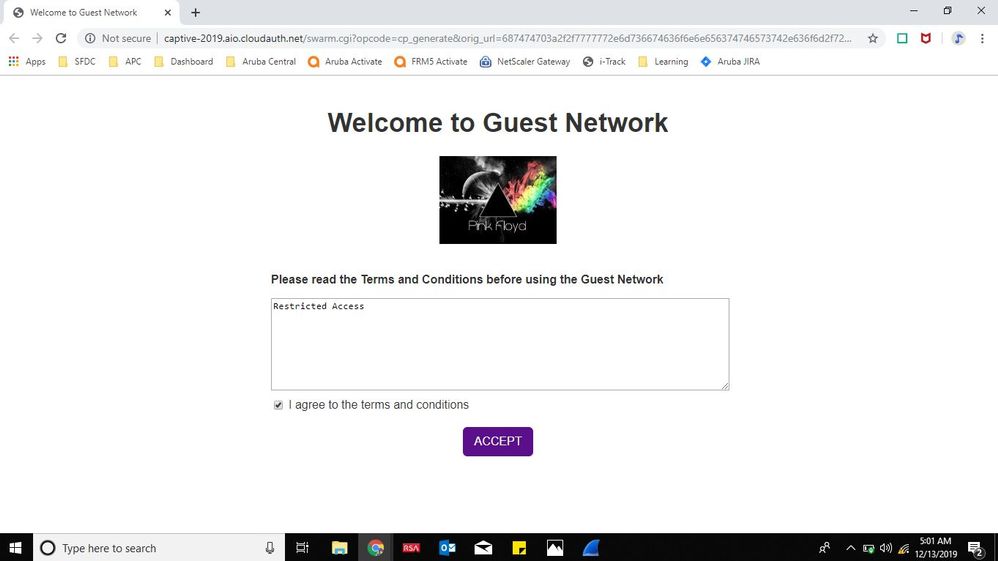 Captive Portal page Hosted on the Guest Client by the AP
Captive Portal page Hosted on the Guest Client by the AP
- Once the Client Device clicks on Accept, the browser will send a HTTP Post, acknowledging the Captive Portal Authentication.
- When the AP receives this HTTP Post, it authenticates the Guest Client and provides access to the Internet.
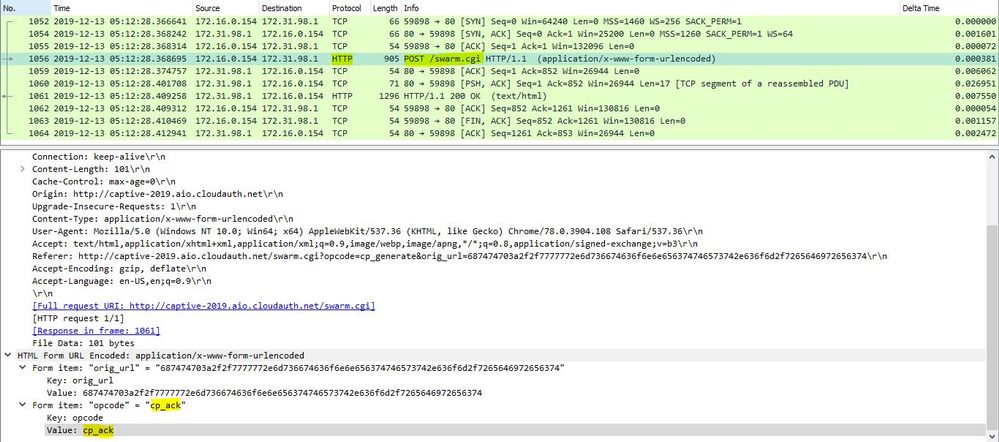 HTTP stream when Guest Client clicks on Accept Button on the Captive Portal Page
HTTP stream when Guest Client clicks on Accept Button on the Captive Portal Page
- Once the Authentication is complete, whenever the Guest Client contacts msftconnecttest.com, the AP will not spoof the TCP connection.
- The Guest Client will hence not get a 302 redirect message from msftconnecttest.com, but will get a HTTP 200 Ok.
- The Guest Client will then assume that there is no Captive Portal Authentication configured on the Wireless Network or the Captive Portal Authentication is successful.
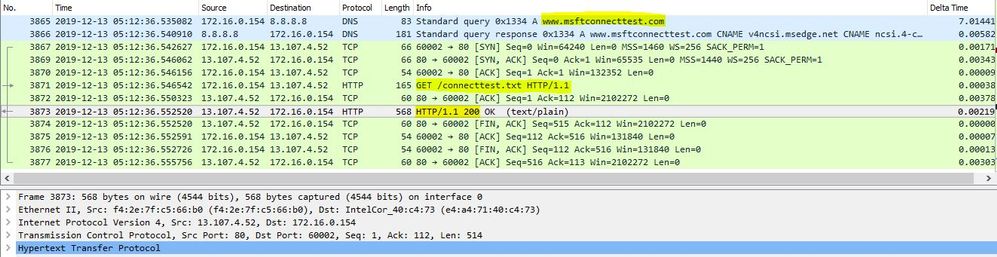 Guest Client checking for Captive Portal Login post Authentication
Guest Client checking for Captive Portal Login post Authentication
#WebbasedAuthentication#ArubaInstantOn#CaptivePortalAuthentication#InternalCaptivePortal#guestnetwork